How to protect your privacy online: 15 essential ways in 2025

Online privacy protection is vital to safeguarding your finances and personal data. Information is one of the most valuable commodities, and the more you expose, the more you’re at risk. The consequences of data exposure range from mild annoyances such as ad targeting to major issues such as depleted bank accounts and social blackmail.
In 2022 alone, online scammers swindled Americans out of $10.3 billion – the most in five years. Moreover, 67% of identity theft victims face a complete digital takeover. As online scams get more sophisticated, the onus is on you to keep your information safe. Here’s how to protect your privacy online.
What is online privacy protection?
You don’t want other people, companies, or the government to access and use your data without your explicit consent, and you certainly don’t want your private information exposed to criminals. When you go online, they’ll try to collect your:
- Name, home address, phone number, and email address
- Demographics such as age, gender, job title, income, and homeownership status
- Social Security number
- Banking and credit card information
- Website and app passwords
- Browsing activity and shopping behavior
- Photos
- Religious affiliation
- Civil group support
- Location
- Search engine history
Online privacy protection, then, refers to actions taken to safeguard your data and control who can access it. Without online privacy protection, your finances and personal life are at risk, so it’s critical to secure your information from hackers and scammers. The next section describes how to protect your privacy online.
How to protect your online privacy (15 ways)

1. Opt out of people-search sites
A study by Duke University found that data brokers collect thousands of data points on U.S. individuals. People-search sites make some of this information publicly available for free, and more detailed information is packed into comprehensive background reports and sold for a fee.
Duke researchers cite the potential for civil rights violations and even physical danger when data brokers and people-search sites share information such as civil group support, religious affiliation, real-time GPS locations, and home addresses.
Duke’s Cyber Policy and Gender Violence Initiative calls Internet privacy a matter of life or death, as these websites can expose the addresses of domestic violence victims to their abusers. In another example, a hate group could purchase dating app information and instantly know the current locations of LGBTQ community members.
However, marginalized groups aren’t the only ones vulnerable. All of us should remove private information from data brokers, as personal details can be used by cybercriminals to steal an identity or create a brand-new one, called a synthetic identity, to commit crimes in the victim’s name.
Having details such as your home address and phone number shared on people-search sites might seem mundane and harmless. In reality, exposing even the most basic details can lead to grave outcomes, especially when anyone – be it a former employee holding a grudge, an unsatisfied customer, or an ex-partner – can easily track you down, stalk you, dox you, or engage in other malicious activity.
This is why the first step to protecting your privacy online is to opt out of people-search sites that sell information to businesses, the government, and criminals. Unfortunately, these websites make opting out tedious, complex, and time-consuming – on average, it takes around 360 hours to remove records from just 20 sites, and you have to re-check them every month to keep your data safe. Onerep can help you save time and ease your nerves by doing all the hard work for you. We monitor 231 people-search and data broker sites to locate your profiles, send opt-out requests on your behalf, and verify each opt-out to make sure your information is truly gone. Then, we continually monitor these websites in case a new profile pops up. All you have to do is sit back and watch.
2. Share as little as possible
Limit what you share everywhere because it’s not always evident where information is leaked. Such was the case with a Fordham University student who had to pay $10,000 out of pocket after her FAFSA application was declined when scammers destroyed her credit, and an Ohio woman who discovered that a fraudster was living a luxurious lifestyle in her name – and on her dollar.
The less information you share, the smaller your digital footprint, and the less data criminals can collect, expose, and use against you.
- Don’t share personal info in emails or texts: Never share account numbers, passwords, credit card numbers, medical information, or images of your driver’s license via email or text
- Watch what you post on social and chat apps: The same rules apply to social media platforms and chat apps. Avoid posting about vacations, family member names, car and banking information, schools you attended, or your birthday – anything you wouldn’t want to fall into the wrong hands. Also, never geotag posts
- Input only required form data: When registering for accounts or filling out online forms, skip any fields that aren’t required. If you want to hide your identity, consider creating guest accounts or using a pseudonym and temporary email address from a service such as Temp Mail
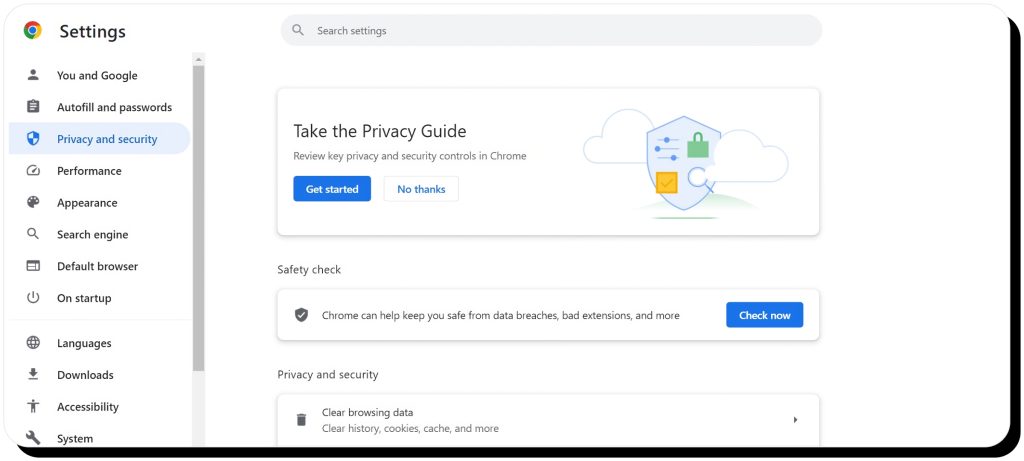
3. Update browser and account privacy and security settings
One of the best ways to protect yourself against online threats is to prevent companies from collecting your data in the first place. Start by updating the privacy settings on your browser and online accounts to minimize your digital footprint and prohibit as much data collection and tracking as possible.
Look for browser and account settings that allow you to:
- Enable Safe Browsing in your search engine
- Disable location tracking
- Hide and restrict your profile information
- Disable data sharing with third-party entities
- Block third-party cookies
- Force your browser to use secure connections
- Disable form autofill
- Automatically clear browsing history, search engine history, cache, and temporary internet files after each use
- Disable prediction services
- Prevent your browser from sharing diagnostic and usage data
- Disable ad personalization
These links provide privacy setting overviews for popular browsers:
You can also use incognito for private browsing mode (though it still allows tracking) or use a secure browser such as DuckDuckGo, Brave, or TOR.
4. Update social media privacy settings
Protect your data from prying eyes by updating your social media privacy settings so that only permitted friends can view your posts, photos, and other information. Look for settings such as:
- Who can see your posts, comments, and likes
- How people can find you (by username/ phone number/ etc.)
- Data settings
- Ad preferences
The best strategy is to restrict access as much as possible. Find more information about social media privacy settings in these links:
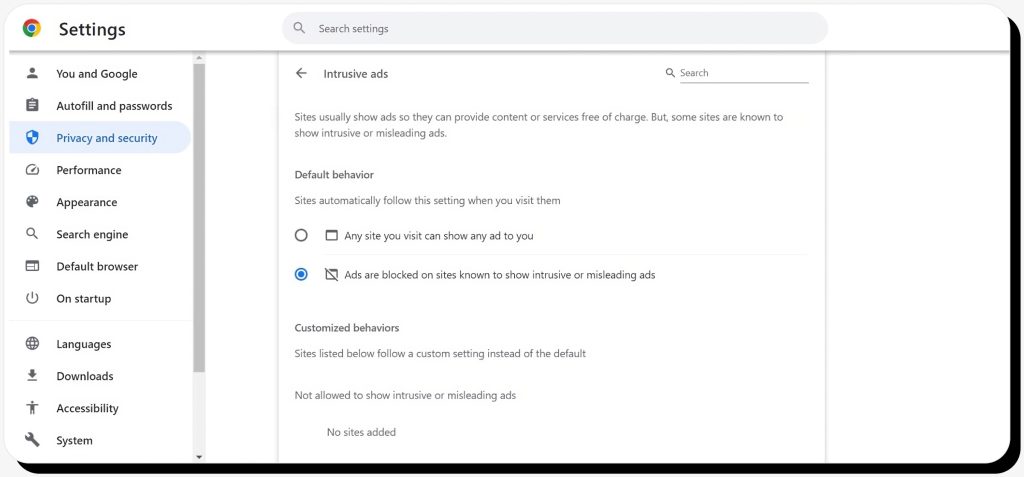
5. Use an ad blocker
Ad blockers help protect your Internet privacy by disabling ads and blocking trackers from monitoring your online activity. Many ad blockers work on computers and mobile devices, and each has its own unique features, such as allowing “acceptable” ads, blocking trackers only, or bundled VPNs. Some are free, some are freemium, and others are subscription services.
Popular ad blockers include:
6. Install antivirus software & enable your firewall
An errant click on a malicious email or advertisement can lead you to unwittingly install malware on your computer. These programs can:
- Track and control your computer
- Record your keystrokes to capture sensitive information
- Automatically redirect you to spoofed scammer websites to steal your data
- Find, steal, and delete your files
The best defense against malicious software is antimalware, antispyware, and antivirus software, which scans your computer for threats so you can quarantine or remove them. Modern Windows operating systems come with Windows Security and Mac OS features built-in protection, and that’s probably enough for most users.
If you want an extra layer of protection, however, you can consider the following options:
- McAfee
- Malwarebytes
- Bitdefender
- Norton
- AVG
- Kaspersky
- Avast
You should also make sure your firewall is enabled to block unauthorized users from accessing your system.
7. Use a Virtual Private Network (VPN)
A secure VPN masks your IP address and disguises your location to prevent your Internet Service Provider (ISP), the government, and others from tracking your online activities. Many VPNs also encrypt your data, so hackers can’t understand it even if they do intercept it.
VPNs are useful for private browsing at home and in the office, and they’re particularly effective at keeping you safe on public WiFi networks. That said, anything you post online can still be seen; for example, if you make a public Facebook post, anyone can see it.
Not all VPNs are created equal. Free VPNs are likely to track and sell your data themselves – so you should avoid them – and some VPNs are susceptible to hacking. In 2021, hackers infiltrated three Android VPNs to sell the records of around 21 million users. That underscores the importance of choosing a reputable VPN service.
Popular options include:
- Nord VPN
- Express VPN
- Surfshark
- Proton VPN
8. Use strong passwords and 2FA – and avoid single sign-on (SSO)
Hackers love weak passwords, and they employ various tactics such as brute force attacks, credential stuffing, and password spraying to steal them.
Create long, complex passwords that aren’t based on real words and employ a combination of uppercase letters, lowercase letters, numbers, and special characters.
An 8-letter password has 209 billion possible combinations, yet computers can crack it in no time. However, a 12-character password with at least one uppercase letter, lowercase letter, number, and symbol would take a computer 34,000 years to crack.
Create strong passwords with a password manager or online generators such as:
Change your passwords frequently and never reuse them between websites, apps, and services.
In addition to strong passwords, you should set up two-factor authentication (2FA) for as many important accounts as possible. 2FA adds an extra layer of security by requiring you to authenticate your login with a second step.
Examples include:
- Passwords sent via text message, email, or phone calls
- QR codes
- Authenticator apps, such as Google Authenticator and Microsoft Authenticator
- Security keys
2FA can protect you if a hacker gains access to your login credentials. When the hacker tries to log in, you’ll receive a 2FA notification. If you don’t complete the next step, the hacker won’t be able to get into your account.
You should also avoid using single sign-on (SSO) services provided by Google, Facebook, and other companies. SSO is convenient because it allows you to instantly register and log in to accounts without filling out registration forms, but they have a significant flaw. If a hacker gains access to your SSO account, they can get into every account you’ve used it with.
9. Keep your software updated
No one likes to restart their mobile device or computer and wait for the system to update, and software update notices seem to pop up at inconvenient times. However, operating system, browser, and software updates often include security patches that close known vulnerabilities.
If you ignore the updates, you’re more susceptible to hacks and your online privacy is at risk. Never ignore software updates – protect yourself by updating software, operating systems, apps, and browsers as soon as possible. When available, allow your software to update automatically.
10. Disconnect third-party applications
Many people connect their Google and Facebook accounts to third-party apps, but that can create a pathway for hackers to steal your information. Often, these connections are long-forgotten and no longer needed, so take a few minutes to review connected apps and disconnect any you don’t need.
Here’s where to find third-party app connections for popular platforms:
11. Use secure payment methods
Exposed banking and credit card information is one of the fastest ways for scammers to steal your money and wreck your finances. Keep your financial information out of the wrong hands by:
- Only paying via secure connections: Check for the padlock near your browser’s address bar to make sure the site is encrypted
- Using payment methods that do not share your financial information with merchants
Even on secure sites, you can’t control what happens to your payment information post-purchase. If the merchant is hacked, your financial accounts could be exposed. Credit and debit cards are generally considered safe because they offer fraud protection, but if your credit card number is leaked, you’ll need to get a new card, update payment information on your accounts, and potentially put a freeze on your credit – which could impact your ability to get loans.
A better option is to use payment methods that do not share your financial information with merchants. Examples include PayPal, virtual credit cards, and digital wallets.
12. Always use a secure connection
The rise of remote work makes this tip more important than ever, as millions of people work in coffee shops, coworking spaces, hotels, and other public areas. Many of these spaces use public WiFi, so your information can be accessed by others on the network. In addition, nearby scammers can use Bluetooth to hack your devices and steal your information.
A secure VPN can help keep you safe on public Wi-Fi by encrypting your data so it can’t be read if it’s intercepted. You can also use a private hotspot and turn off Bluetooth to stay safe when you’re working in a public space.
13. Familiarize yourself with common scams
Another good way to protect your online privacy is to be aware of the latest scams. Some of the most common scams today include:
- Bank impersonation and “fraud alert”
- Bonus “gifts”
- Fake package delivery issues
- Account “security” alerts
- Fake job offers
- Phishing and smishing
- Pop-up ads warning of computer malware
The more you know about how scams work, the easier it is to recognize them and prevent them.
14. Educate your family
Though you might be aware of online scams and know how to protect yourself, your spouse and children might not. This is especially true if your children have smartphones or tablets and routinely download games or are active on social media sites. Hackers could gain access to your own accounts if they trick your kids into sharing your data or downloading malicious software.
Be sure to secure all your family’s devices and accounts, not just your own, and create a set of rules to help family members avoid sharing personal information online.
15. Protect all your devices, apps, and accounts
When you’re thinking about online privacy protection, you probably think about your desktop computer, laptop computer, tablet, and mobile phone – but there are many more connected devices today. The Internet of Things (IoT) presents opportunities for hackers to steal your information where you least expect it – smart TVs, fridges, thermostats, printers, home hubs, and other gadgets may record your conversations, prompt you to share personal information, or allow you to download suspicious apps. Be careful about what you download and share with all your devices.
Safeguarding personal devices
Digital privacy concerns aren’t limited to web browsing. Your personal gadgets are also at risk, so it’s critical to safeguard desktop and laptop computers, smartphones, tablets, and smart devices. Here are a few more steps besides the ones mentioned above for setting up security features on all your devices.
Computers (desktop and laptop)
- Add a screen lock password or other authentication
- Create regular backups
- Turn off Bluetooth when not in use
- Encrypt data
Mobile devices
- Secure your lock screen and disable lock screen notifications
- Review and revoke unnecessary app permissions
- Uninstall unnecessary apps
- Enable the Find My Device feature and remote wipe
- For messaging, use an encrypted app with end-to-end encryption
- Disable NFC when locked and turn off Bluetooth when not in use
- Turn on mail privacy (Apple)
- Only use official app stores and enable Play Protect (Android)
- Limit location services
Smart home devices (Internet of Things)
- Segment your network so that IoT devices don’t share the same network with other devices
- Keep IoT software up to date
- Disable unnecessary features
How your data is used
Your information gets online in various ways, from account registration forms and app downloads to social posts, search engine queries, and data breaches. Businesses use cookies (small files that store information about your website visits) and other methods to track your shopping and private browsing activity, then use that data to serve targeted ads and offers they think you’re likely to respond to.
Some argue that targeted ads create a more tailored, enjoyable user experience. That might be true, but the practice also leaves your data at the mercy of whomever collects it. Eighty percent of companies store sensitive data in the cloud at a time when data breaches continue to increase.
The federal government states it collects and uses personal information in “increasingly sophisticated ways” for law enforcement, border control, and “enhanced online interactions,” and 64% of Americans are concerned about how the government is using that information.
Data brokers collect and sell information to anyone willing to pay for it, prompting civil rights concerns. Criminals with nefarious intent may collect information on their own or purchase it from data brokers and use it to scam unsuspecting victims. They can sell your private information on the dark web or use it to:
- Commit identity theft
- Deplete your bank accounts
- Take out loans in your name
- Open up credit card accounts
- Purchase vehicles
- Lease apartments
- Rack up high phone bills
- Book vacations
- Open online accounts
- Hack your social media accounts
- Publish your dating app activity
- Get medical care
- Apply for government benefits or official documents, such as a passport
Businesses, the government, and criminals are consistently coming up with new ways to use your data, underscoring the need to know how to protect your privacy on the Internet. Consequently, you should learn more about current trends in online privacy and what’s on the horizon in this ever-evolving landscape.
Current trends in online privacy
Current trends in online privacy include:
1. Centralized privacy management for online accounts
As consumers demand more control over their data, companies are catering to that demand with centralized privacy management. Website visitors can choose which data is tracked and stored – or opt out of online tracking entirely – from a single, centralized location. The overarching idea behind privacy UX (user experience) is to make it easy for users to understand and control how companies collect and use their data.
2. Artificial intelligence
AI presents many possibilities for online privacy – some good, some bad. For example, AI could be employed to collect detailed user demographic and behavior insights. On the other hand, AI could also make data collection anonymous.
3. Privacy by design
Privacy by design refers to the practice of incorporating privacy features into products and services. There are seven foundational principles of privacy by design:
- Proactive, not reactive: Anticipate and prevent privacy issues
- Privacy by default: Users do not need to opt-out to have full privacy protection
- Privacy embedded into design: Privacy controls permeate design rather than being added on later
- Full functionality: Privacy protection should not limit how a product functions
- End-to-end security: Protect privacy throughout the entire lifecycle
- Visibility and transparency: Clearly communicate privacy practices with all users and share responsibility for privacy protection
- Respect for user privacy: Prioritize user interests, not business interests
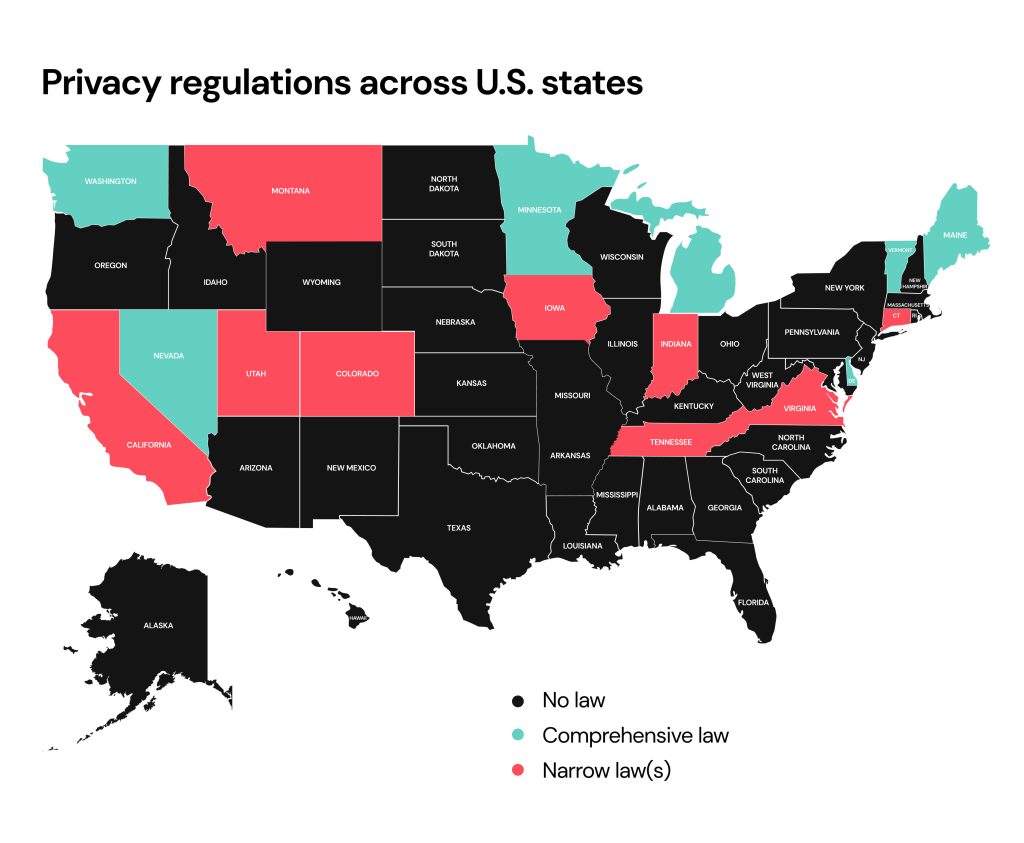
4. More regulations
Experts predict more privacy-focused regulations worldwide, and several U.S. states have recently adopted or introduced privacy legislation. With legislation comes enforcement, and another current trend is an increase in Data Subject Access Requests and complaints. Individuals can file DSARs with organizations to see what data they’re collecting about them and to verify that they’re using their data legally.
5. New tracking technologies
Websites are replacing third-party cookies with advanced online tracking technologies. In 2021, Google introduced Federated Learning of Cohorts (FLoC), but the technology faced heavy criticism from privacy advocates. FLoC has since been replaced with Topics, which monitors your browsing history to identify your interests so Google and its partners can serve you targeted ads. While some argue against any kind of online tracking for ad personalization, others say that without a privacy-first tracking mechanism, advertisers will resort to shady tracking activities.
Privacy laws and regulations
The United States does not have an all-encompassing privacy law like Europe has in its General Data Protection Regulation (GDPR). However, other laws do provide online privacy protections in specific circumstances, including:
- HIPAA: Covered entities and their business associates must safeguard Protected Health Information (PHI)
- Fair Credit Reporting Act: Protects confidential information on consumer credit reports
- Gramm-Leach-Bliley Act: Financial institutions must explain how they share information and protect sensitive data
- Electronic Communications Privacy Act: Governs how law enforcement can obtain electronic communications; for example, one provision is that a warrant is required to intercept emails in transit
- Video Privacy Protection Act: Originally passed to prevent video rental companies from disclosing which movies individuals rented, this act has spurred lawsuits against video streaming services that share viewing history with third-party companies
- Family Educational Rights and Privacy Act: Protects student education records
- Children’s Online Privacy Protection Rule: Requires parental consent for organizations to collect information about minors aged 13 and under
- Federal Trade Commission Act: Requires organizations to employ appropriate security standards and to make good on any privacy protection claims
- Privacy Act of 1974: Governs how the U.S. government can collect and store data and grants individuals the right to view the data collected by the government
In addition, several U.S. states have enacted comprehensive privacy laws. These laws generally govern how businesses can collect and sell personal information and grant individuals the right to access their information and/or request that businesses correct or delete records.
Several other states have enacted narrower privacy protection legislation. Eleven states have introduced privacy protection bills, and though all privacy legislation helps, privacy advocates remain concerned about data collected by organizations that operate in multiple states – or even in other countries.
Ultimately, the onus is on you to protect your privacy online. Follow the 15 strategies outlined here to stay safe and keep your private information out of the wrong hands.
FAQ
How do I keep my online private?
Use a VPN for private browsing, install ad blockers and anti-trackers, use incognito mode (or a privacy-first browser), and regularly install updates on your operating system and software to help keep your online activities private.
Is it possible to protect your privacy online?
Yes, but even though there are some laws designed to protect your privacy online, the responsibility to safeguard your personal information resides with you.
How can you protect your online identity and privacy?
Opt out of people-search sites, familiarize yourself with phishing and smishing scams, set up alerts with your banking and other accounts to notify you about suspicious activity, and consider using identity theft and privacy protection software to protect your online identity.
Why is online privacy important?
Online privacy helps you control who collects and shares your information. Without it, your data could be published online, used to track your behavior, or captured and sold on the dark web to scammers who could steal your money or blackmail you.
How are we tracked online?
Browser cookies, spyware, malware, viruses, apps, social media posts, pixels, IP addresses, account tracking, web beacons, browser fingerprinting, and location services are all ways we can be tracked on the Internet.
How to protect your privacy on social media?
Be careful about what you post and adjust your settings to limit who can see your posts and personal information. Additionally, adjust the settings on what information social media platforms themselves can collect and share about you.
How to protect personal information online?
Share as little information as possible – the less you share, the less you're at risk. Be careful about what you post on social media and only fill out required form fields when creating new accounts. Adjust social and browser privacy settings to restrict access to your information, use two-factor authentication, and always use strong passwords to protect your personal information online.
Is using a VPN legal and safe?
Yes, reputable VPNs are safe and legal in most countries, including the United States. However, some countries – such as Russia, North Korea, and China – restrict or ban their use.
How do hackers steal personal information online?
Hackers employ various tactics to steal your personal information, including phishing scams, malicious advertising, social engineering, brute force attacks, WiFi hacking, and malware.
Are browser extensions safe for online privacy?
Browser extensions downloaded from official sources, such as the Google Chrome Web Store, are generally safe – but there will always be risks associated with installing third-party extensions. Before installing any extension, check its privacy policy, make sure it’s from a reputable developer, and ensure it has many positive reviews.
How do I know if a website is secure for online transactions?
Make sure the URL begins with https, which indicates the site has an SSL certificate and encrypts transactions. Some web browsers have a padlock near the address bar. Click on it to verify that your connection is secure and the certificate is up to date. Of course, that only means the site is secure – not that the transaction is safe, so only buy from reputable companies. You can dig deeper with a tool like Google’s Safe Browsing site status checker to ensure the site is legitimate.
Can I remain anonymous while browsing the Internet?
No, you can’t remain completely anonymous online. Even when you take measures to protect your privacy, you’re still sharing unique identifiers such as your browser configuration. However, you can mask a lot of data and minimize your digital footprint by taking a few steps.
What steps can parents take to protect their children’s online privacy?
Parents can educate their children about online privacy, create family safety rules, use parental control apps, monitor social media accounts, and double-check privacy settings on kids’ devices, apps, and accounts.





Dimitri is a tech entrepreneur and founder of Onerep, the first fully automated data removal service. Top cybersecurity CEO of 2021 by The Software Report.