
In 2022, the U.S. Department of Health and Human Services fielded healthcare data breach reports that exposed the Protected Health Information of more than 48 million Americans. That represents a 21% increase over 2021 and underscores the importance of safeguarding PHI as healthcare data breaches continue to affect more Americans year over year.
This article details what PHI is, how it is regulated, and why data privacy and security are critical for healthcare professionals, caregivers and patients.
What is protected health information (PHI) under the Health Insurance Portability and Accountability Act (HIPAA)?
As defined by the Health Insurance Portability and Accountability Act of 1996 (HIPAA), Protected Health Information, or PHI, is the personal health data collected by covered entities that can identify a person.
This data is also known as individually identifiable health information (IHII) and may come in any format, including oral, paper and electronic. The electronic form of this information is known as ePHI (electronic protected health information). Virtually, all of our data is ePHI, as almost all medical records are stored electronically.
Examples of PHI
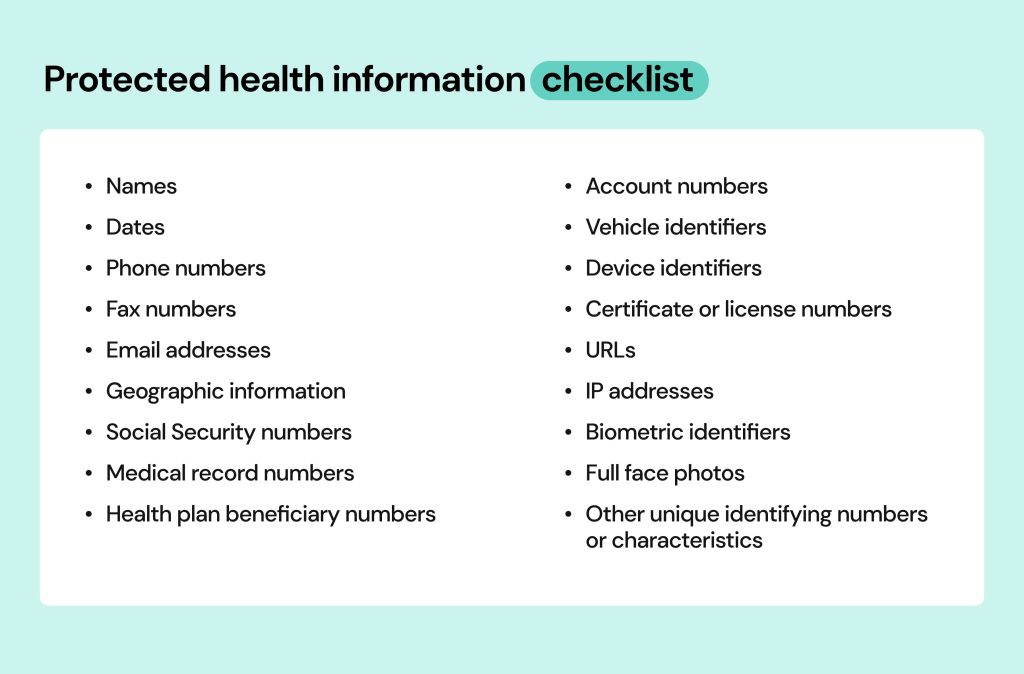
As stated, Protected Health Information is any data that identifies a patient to their medical records. HIPAA outlines 18 such identifiers that might be found in a designated record set, including:
- Names
- Dates (such as admission date or birthday)
- Contact data (phone and fax numbers, email addresses)
- License plate number and other vehicle identifiers
- Geographic information (including street address)
- Social Security number
- Health plan beneficiary number
- Account number
- Device identifiers (such as serial numbers)
- Web data (URLs and Internet Protocol addresses)
- Biometric identifiers (such biometric data as face scans and fingerprints)
- Full face photos
- Medical record numbers
- Any other unique identifying number, characteristic or unique code assigned to a patient
Note that many of these details can also be considered PII (Personally Identifiable Information). Such bits as your name, address, contact data, or Social Security number may be considered PHI and PII at the same time. What’s important to understand is that once on a medical record, PII becomes PHI and starts being protected by HIPAA. So, if your personal information is leaked through a data breach of a hospital – it is investigated by HIPAA. If the same bits of personal information are leaked through an attack on your company, it is investigated by other entities.
How is Protected Health Information used?
Protected Health Information is used during various stages of health care and in different circumstances. Cases range from identifying patients, monitoring medical histories and delivering treatment in a healthcare setting to sharing important medical insights with other providers, such as other doctors and hospitals, and billing patients for treatment. PHI may also be used to conduct research when approved by an Institutional Review Board (IRB), such as sponsored clinical trials submitted to the Food & Drug Administration. Basically, any activity that concerns your health history will require using PHI.
What isn’t considered protected health information?
If the information can’t be used to identify you or doesn’t come from a covered entity, it isn’t considered PHI. In these cases, your information isn’t covered by HIPAA.
For example, an EKG strip without personal information wouldn’t be considered PHI. However, if that EKG strip listed a patient’s account number, it would be considered PHI.
As mentioned before, if it can be used to identify you but isn’t connected to health data, it’s considered PII (personally identifiable information).
Why is it important to protect PHI?
From a consumer point of view, PHI includes a lot of private and sensitive details. Exposure of this information can be dangerous, potentially leading to stolen identities, credit fraud and blackmailing. In one incident, a thief used stolen medical records to impersonate a patient and rack up over $20,000 in medical bills in that patient’s name. The victim was still dealing with the fallout 15 years later, worrying that hospital records might list the thief’s blood type instead of his own.
For organizations, disclosing this critical data can lead to arrests, loss of reputation, loss of jobs, and lost trust. Violations can also prove costly. In February 2023, Banner Health paid a $1.25 settlement for a data breach that disclosed the PHI of nearly three million people. That same year, Yakima Valley Memorial Hospital paid a $240,000 HIPAA settlement after security guards illegally accessed 419 patient records.
Another reason to safeguard PHI is its high value on the black market. Medical records can sell for as much as $1,000 on the dark web. In comparison, credit card numbers sell for around $5 and Social Security numbers for only $1. This shows how much of a treasure health data is for cybercriminals and how much they are ready to pay for it.
Moreover, even if one’s PHI doesn’t make it all the way to the black market, it will still end up on data brokers and people-search sites in case a data breach occurs. These sites are notorious for collecting people’s personal information through various means and sharing it with just about anyone who looks you up, often for free.
Subsequently, it benefits organizations, the people they manage and patients themselves to handle PHI properly. Companies can start by following HIPAA’s guidelines.
How does HIPAA protect PHI?
HIPAA, or the Health Insurance Portability and Accountability Act, protects PHI by establishing standards for using and disclosing it. HIPAA is managed and enforced by the Office for Civil Rights (OCR) under the US Department of Health and Human Services.
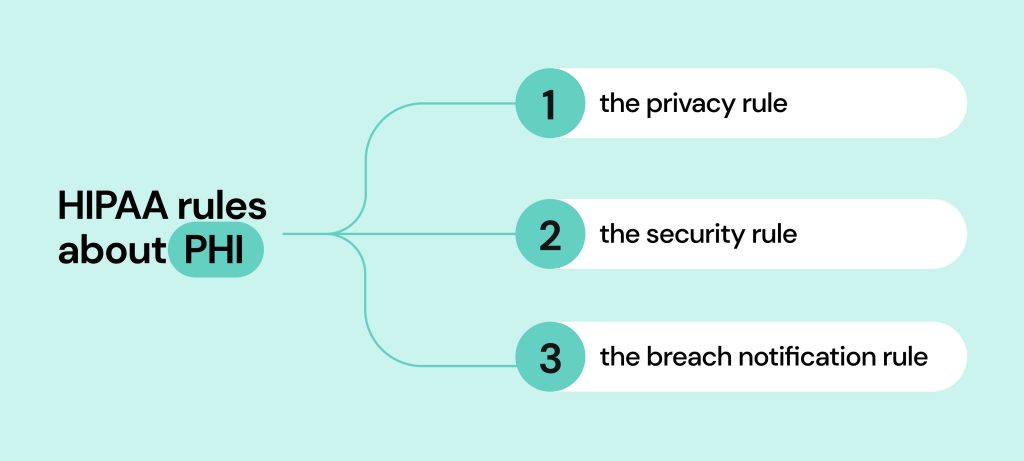
HIPAA rules can be broken down into three areas of focus:
- The Privacy Rule
- The Security Rule
- The Breach Notification Rule
Who is subject to HIPAA’s rules about protected health information?
The HIPAA rules apply to covered entities and business associates and detail how they can use or disclose PHI. “Use” essentially means to use PHI internally, such as in directing patient care, and “disclose” means to share PHI with a third party, such as another healthcare provider, business associate or research team.
Covered entities and business associates include:
- Healthcare providers (doctors, hospitals, nurses, clinics)
- Health plan providers (health insurance companies, HMOs, Medicare, Medicaid, and other health plans that handle consumer health information)
- Health care clearinghouses (companies that reformat nonstandard data received from various entities into standard data HIPAA elements and vice versa. Examples include billing services and repricing companies)
- Third-party business associates (individuals or organizations that provide billing, medical claims processing or attorney services on behalf of a HIPAA-covered entity)
The HIPAA Privacy Rule
The HIPAA Privacy Rules require a covered entity to have safeguards to protect the use and disclosure of private health information. Simply put, it requires authorization before any information is released and heavily limits the information to be accessed only when necessary.
Here are a few examples of the privacy rule in action:
- Individuals can get a copy of their health records for examination, transfer data to an approved third party, and ask for corrections if necessary.
- Businesses using this data must enter a HIPAA Business Associate Agreement (BAA). BAAs require business associates to follow the same medical data compliance requirements as insurance companies or hospitals.
- Entities must implement access controls so that only those who need the data (like your doctor) can access it.
- Regular audits of access controls and related systems must occur, and these procedures must be documented.
The Privacy Rule was applied before the advent of modern technology. To enhance medical data protection, HIPAA needed to introduce the next rule.
The HIPAA Security Rule
HIPAA privacy rules required a massive update to combat growing cybersecurity threats. Healthcare trends showed that many medical facilities were going digital. This introduced the need for improvement in the form of The HIPAA Security Rule.
Under the HIPAA Security Rule, a covered entity must:
- Ensure all ePHI is secure yet available to patients
- Protect against security threats
- Protect against impermissible uses or disclosures
- Maintain workforce compliance
Caregivers can adopt multiple practices that help safeguard ePHI, including:
- Securing network and communications systems to prevent hacks and other cyber attacks
- Implementing user access policies that prevent unauthorized access to patient medical records
- Training staff on HIPAA laws and how to protect ePHI
One of the rule’s goals is to protect patient information while allowing caregivers the flexibility to implement new technologies that improve healthcare operations, quality and efficiency.
The final piece to HIPAA’s modern overhaul was the Breach Notification Rule.
The HIPAA Breach Notification Rule
The HIPAA Breach Notification Rule requires covered entities and business associates to report any PHI breaches to affected individuals, the U.S. Department of Health & Human Services and, in some cases, the media. These notifications must include the following factors:
- The data that was breached (including how it happened, the amount of data lost, and the likelihood of it happening again).
- The parties involved in the potential disclosure (including any unauthorized persons and affected parties)
- How this issue was mitigated (and how it will be mitigated going forward)
Breach notification requirements also dictate the steps that need to be taken depending on the size of the breach:
- If ten (or fewer) people were exposed, written or telephone notice must be given to the affected parties.
- If 500 (or more) people were exposed, businesses must notify the local media within 60 days.
- In both cases, the company responsible for the breach must fill out an electronic breach form to report to The Secretary
This three-pronged approach ensures that anything considered protected health information is safeguarded and secured, and (if necessary) the corresponding entities are notified should a breach occur.
Who is excluded from HIPAA’s rules?
If you were to share health data with a good friend, it wouldn’t be covered under HIPAA rules. The friend is not a HIPAA covered entity. The same could be said if you provide personal health information to health-tracking software like Fitbit.
Other organizations that aren’t required to follow the privacy and security rules established by HIPAA include the following:
- Life insurance companies
- Employer (privacy rules do not apply to employment records)
- Workers’ compensation companies
- Some non-healthcare government agencies (schools, state, law enforcement, and municipal offices).
- Research providers (as long as you know your data is being used for such)
Generally speaking, your health care providers cannot give away protected health information to your employer (or most third parties) without your permission. Regarding workers’ compensation claims, there must be an exceptional reason to request your medical data.

What are allowable uses and disclosures of PHI?
When protecting PHI, it helps to know what health care entities can use data for. There are circumstances in which they’re permitted (though not required) to use and disclose PHI to a public health authority or to another HIPAA-compliant covered entity or business associate without patient authorization. They include:
- Treatment and healthcare services
- Quality assessment and improvement
- Clinical guideline and protocol development
- Patient safety activities
- Case management and care coordination
- Contacting other doctors and patients about alternative treatment options
- Staff performance evaluations
- Training programs
- Compliance programs and fraud and abuse detection
However, the following conditions must be met before one covered entity can share PHI with another one:
- Both must have relationships with the patient
- The shared PHI must be relevant to those relationships
- The sharing entity must only disclose the minimum information necessary
How do you report a PHI breach?
If you believe your PHI was illegally used or disclosed or that your rights under HIPAA were otherwise violated, you can file a complaint with OCR. You can also make complaints via mail, fax, or email.
When reporting a PHI breach, be sure to include the following information:
- Name
- Full address
- Telephone number (with area code)
- Email address
- Information on the organization or individual who you believed violated health information privacy rights
- A description of how those privacy rights were violated
- Your signature and the date of the complaint
These complaints will go directly to the OCR; you can get more instructions here.
How can patients prevent individually identifiable health information from leaking?
It’s important to note that the responsibility to protect individually identifiable health information doesn’t lie with healthcare providers alone but with patients as well. Such actions as sending a medical bill or test results via email may seem common and harmless. But in reality, they can lead to grave outcomes in case this data is stolen.
Just like organizations, patients must treat their own medical data with due care. Here are several recommendations to follow:
- Share individually identifiable health information only with trusted people and entities.
- Don’t shy away from asking medical establishments what policies they have in place to protect your data.
- Do your research and turn only to HIPAA-compliant entities for a health care service.
- Encrypt medical documents if you need to send them via email or messenger. That way the person receiving the doc will be able to open it only with a password.
- Securely dispose of any records, both printed and digital.
- Don’t store medical data on your devices without encryption.
- Use strong passwords on all devices and keep them locked when not in use. The same applies to all online accounts you open.
- Don’t use public Wi-Fi and access the internet only with a VPN connection. It will help you hide your IP address and protect web data.
- Delete your personal data from people-search websites and adjust the privacy settings on your social media accounts. This will prevent criminals from gluing your identity together piece by piece taken from various sources.
How can Onerep help?
With Onerep, you can keep your personal information private by removing it from data broker and people-search websites that sell it online.
Overall, there are more than 400 different data points on people available in their databases. They make a profit by packaging these details into comprehensive profiles about every adult American, and offering them to anyone for a small fee. Besides full names, dates of birth, phone numbers and address history, data brokers store marriage and divorce records, unsealed lawsuits or legal actions, voter registrations, government spending reports, information about relatives, and more. They also add information pulled from social media accounts and commercial sources like retailers, marketing lists, phone directories, web services and apps that collect data on purchases and other consumer behaviors and habits.
Coupled with sensitive information like PHI, people-search websites are a threat to personal security. The reason is simple – criminals resort to these sites as they like to use every way available to them to collect bits of identifying information needed to form synthetic identities, impersonate their victims and commit fraud that results in financial losses for both individuals and organizations.
Onerep helps you protect your personal information by scraping it off data brokers and people-search sites. We scan 316 sites to locate your profiles and send opt-out requests on your behalf. Moreover, we continually monitor the web in case any new privacy-breaching sites and profiles pop up. If they do, we repeat the process over and over to make sure your personal information stays off data brokers for good.
Conclusion
PHI, or protected health information, is the responsibility of all health care industry members. This includes everyone from the company’s CEO to the dedicated medical staff working around the clock to keep us healthy.
As the healthcare industry continues to face cybersecurity threats, hospitals, clinics, business associates, and patients need to understand what Protected Health Information is and how they can prevent it from falling into the wrong hands. To that end, healthcare organizations and patients should familiarize themselves with the rules and rights to keep their medical information safe and secure.
HIPAA always introduces new guidelines, so stay updated on the latest changes on the HHS website.
FAQs
Is a picture of a baby on a wall an example of PHI?
Generally speaking, no. While PHI includes full-face photos, if you have a picture of your baby on a wall (say in your office cubicle), that’s not handled by a covered entity. However, a picture of a baby on a pediatrician’s wall is considered PHI.
What is protected information under HIPAA?
Protected information under HIPAA generally includes any data handled by a health care industry member that could be used to identify you. Examples include a photo of your face, name, and address.
What are the three types of PHI?
The three types of PHI are spoken, paper, and electronic (ePHI). This means that private medical data exposures are considered at multiple levels, with all three forms counting as different violations.
What are three common HIPAA violations?
Some of the most common HIPAA violations include impermissible PHI use and disclosure, inadequate PHI safeguards (including ePHI) and insufficient patient access to their health data.
What is not protected by HIPAA?
HIPAA doesn’t protect any data that doesn’t identify a patient or isn’t handled by covered entities. In addition, many organizations are not subject to HIPAA Privacy and Security Rules, including life insurance companies, law enforcement and employers, so employment records are not protected.
What is the most important rule in HIPAA?
The HIPAA privacy rule is the most important in HIPAA, as it protects individually identifiable health information. The privacy rule is an official legal requirement for everyone who handles medical data to the data owner’s right to privacy.
What are the four standards of HIPAA?
The four standards that HIPAA covers include physical safeguards, administrative safeguards, technical safeguards, and proper information handling procedures. These four standards ensure data is handled properly and managed through secure channels.
What is the basic HIPAA policy?
The 1996 Health Insurance Portability and Accountability Act established a basic policy to protect patients’ individually identifiable health information. It establishes that patients’ private medical data should only be disclosed when absolutely necessary.
What is PHI in cybersecurity?
PHI stands for Protected Health Information. It’s relevant to cybersecurity because covered entities and their business associates must ensure their networks and devices are secure to avoid patient data breaches that could expose PHI.
What value is PHI?
To healthcare organizations, PHI helps doctors, insurance companies, and other professionals conduct business. To regular people, PHI includes personal data that could be used to steal their identity. Moreover, PHI is very valuable on the black market, as medical records can sell for as much as $1,000 on the dark web. In comparison, credit card numbers sell for around $5 and Social Security numbers for $1.




Mark comes from a strong background in the identity theft protection and consumer credit world, having spent 4 years at Experian, including working on FreeCreditReport and ProtectMyID. He is frequently featured on various media outlets, including MarketWatch, Yahoo News, WTVC, CBS News, and others.