What is personally identifiable information (PII): protection tips and insights

There were over 3 million cases of fraud and identity theft last year. Improper use of your personally identifiable information (PII) is the leading cause of these types of cybercrimes. This article explains more about PII and will teach you how to protect yourself.
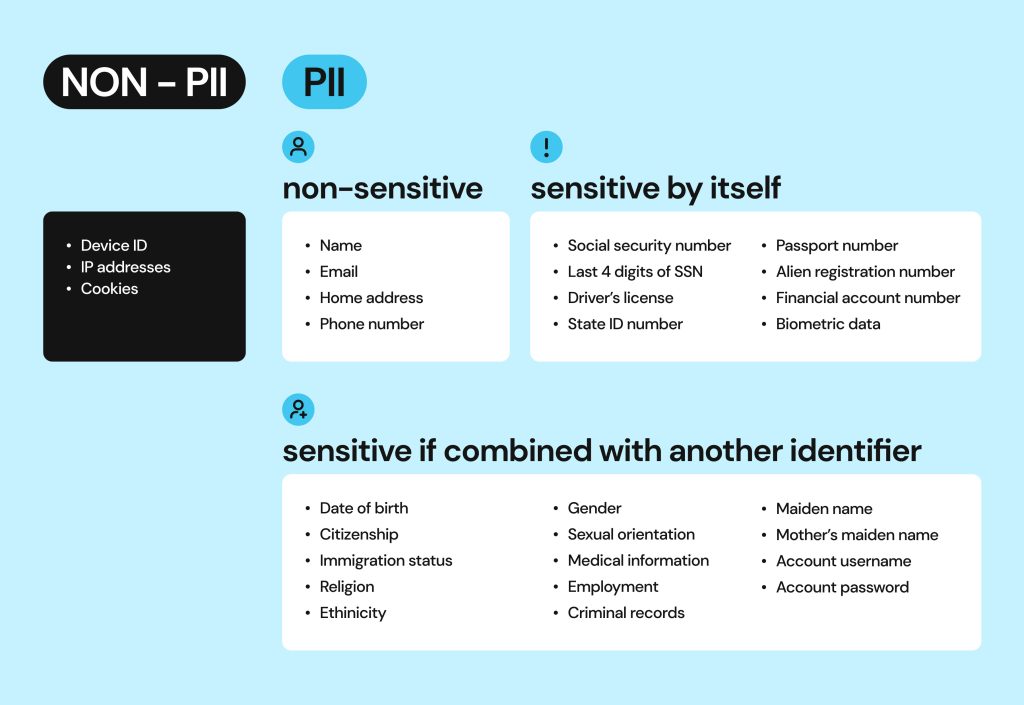
Personally identifiable information (PII) is any information about an individual that can be used to uncover their identity. PII is often divided into sensitive (unique identifiers like SSN, biometric record, or driver’s license) and non-sensitive (poses a risk only when pieced together with other personal details – like name, gender, or birthday). Compromised PII leads to numerous threats ranging from hacked accounts to identity theft and financial fraud.
What is PII?
PII stands for personally identifiable information and refers to an individual’s private data that could be used to discover their identity.
PII can be sensitive and non-sensitive. Someone’s social security number, passport, or driver’s license are unique identifiers and prime examples of sensitive personally identifiable information.
Non-sensitive personal information can become a risk when that data is pieced together to identify a person indirectly. For instance, gender, birthday, ethnicity, or medical history may disclose a person’s identity when combined with other information.
A company may store PII in many ways, but it is most often accessed by cybercriminals when it is available online, e.g. through social media or a public record database.
What qualifies as PII?
Experts often disagree as to which personal identifiers should be considered PII and which degree of sensitivity should be attributed to such elements. The general rule is to evaluate each bit of personal information from the perspective of personal damage it might cause if it were lost or compromised.
Here are some common examples of personally identifiable information:
- *Name: Full name, maiden name, mother’s maiden name, etc.
- *Date of birth
- Personal identification numbers issued by the government: Social Security number (SSN), passport number, driver’s license number, I.D. card, taxpayer identification number, Medicare, or Medicaid.
- Other personal identification numbers: Financial account numbers, credit, and debit card numbers, etc.
- *Contact information: Address, phone numbers, and email addresses.
- Personal characteristics: Biometric information including photos (face and other identifying characteristics), retina scan, fingerprints, handwriting, voice, and facial geometry.
- *Electronic and digital account information: Internet account numbers and passwords.
- School and employee personnel records and I.D. numbers: Any educational records or identification numbers.
*Of note: Identity Theft Resource Center, a distinguished expert in the field of identity protection does not consider names, phone numbers, passwords, or email addresses to be part of PII.
The above list does not show all of the possible PII examples, but it gives you an idea of the types of data that must be protected.
PII sensitivity range
Indeed, PII scope can be confusing, which is why people often ask for the PII meaning or the PII definition. When wondering what is considered personally identifiable information, the answer is the same. It is any stand-alone or combined personal data specific to an individual, which may compromise their identity if it falls into the wrong hands. The important thing to keep in mind here is that PII can become more or less sensitive when combined with other details. For example, name, date of birth, and bank account number become damaging when they are put together.
What is not considered PII?
There is a lot of information about us online that seems personal but is not necessarily sensitive PII. These details are sometimes called non-PII or non-sensitive data.
Some examples of non-sensitive information include:
- *Name
- Place of birth
- *Birthday
- IP address
- Aggregated statistics on the use of services and products
- Cookies
How could a name or birthday be considered non-sensitive information? Because many people share the same name or birthday. By themselves, a name or a birthday is not specific to a person. However, when connected as part of a cache of information about someone, they do become sensitive PII.
We’ve made this infographic to display the personal information spectrum with a specific goal in mind – raise awareness about the risks involved in a simple act of sharing your personal information.
Which PII data is at risk?
The short answer is that it is all at risk. Credit card and social security information can be sold on the dark web also known as the online black market.
What we consider less sensitive data like names, birthdays, contacts, details, employment, and criminal records are on display on social media and people-search sites. Cybercriminals can find these bits and pieces of your PII and combine them to then steal your identity and funds.
How does PII get stolen?
Here are just a few ways that PII can be compromised:
- A lost or stolen wallet containing IDs, credit cards, and/or social security number falls into the wrong hands.
- Data breaches through website hacks or insider information theft.
- Social engineering criminals convince victims to reveal sensitive information or lure them into clicking malicious links that install malware that steals their PII.
- Data transmissions via public or unsecured home Wi-Fi networks enable hackers to steal passwords for banking and shopping accounts.
- Email phishing and phone scams are used to divulge sensitive information.
- Credit card skimming devices steal card numbers and pins.
- Unencrypted websites with weak security allow cybercriminals to intercept your personal information when you use them.
What are the dangerous consequences of PII theft?
When criminals have your PII, they can:
- Scam any financial institution to steal your funds, cash checks, and open new credit cards in your name, etc.
- Steal your tax return or government benefits.
- Apply for loans in your name.
- Log in to your personal accounts (bank, medical, email, social media, etc.) to make fraudulent purchases or scam others.
- Open new phone and utility accounts.
- Change your billing addresses for services and then run up charges.
- Obtain a new driver’s license or official IDs in your name to assume your identity and then use your identity when questioned by police.
- Buy drugs or submit fraudulent bills for medical coverage you did not receive.
PII theft leads to devastating consequences as criminals target a victim’s life. By the time someone realizes what has happened, they may have financial losses, have damaged credit, or even be subject to arrest if a criminal committed a crime using their identity. Child identity theft may go unnoticed for years while creating a mess that needs to be fixed later.
If cybercriminals create a synthetic identity using real PII, such as a social security number combined with fake identifying information, the resulting damage can have severe long-term consequences for the victim causing credit, insurance, tax, and other issues that are difficult to resolve.
How do I protect my PII?
In addition to the security tips we’ve already shared in the above sections, here is a checklist with specific recommendations to follow to keep your PII safe:
- Do not keep your social security card in your wallet.
- Shred or otherwise securely dispose of any printed PII, such as unwanted mailings.
- Avoid storing PII on electronic devices and permanently delete any record of PII you no longer need on a device.
- Create and use strong passwords on all digital devices and keep them locked when not in use. Even if you do not store PII on these devices, you may use them for transactions that contain your private data.
- Keep your social identity to yourself, especially on social media. Use dummy data (contact details, aliases) whenever possible so that your online identifiers can’t be matched to your true identity.
- Use antivirus protection and two-step verification.
- Don’t use public Wi-Fi or let strangers connect to your primary Wi-Fi network.
- Use VPN to protect your data and online privacy. Plus, a VPN allows you to find out which country has the best Netflix. It’s a win-win!
- Don’t click on links in emails or messages from an unfamiliar email address.
- Use trusted third-party payment services, encrypted sites, and other secure methods for entry of any PII.
- Proactively freeze your credit reports to prevent cybercriminals from getting credit with your identity.
- Monitor your accounts for known data breaches. Plenty of services are available to help.
- Read the privacy policy of any service you use to check how they handle your information and whether they share it with third parties.
Applicable laws and regulatory institutions
There are various personally identifiable information laws and federal agencies that protect people’s sensitive PII. The following are some widely-known protection laws that regulate PII handling in the U.S. It’s important to note however that protections are not limited to these rules, acts, and laws.
COPPA
The Children’s Online Privacy Protection Rule (COPPA) details the requirements that online services targeted to children must follow when collecting PII. In some cases, parents of children under 13 may be given choices of what information they want to share with a website. Violation of these regulations may result in large fines and criminal penalties.
HIPAA
The Health Insurance Portability and Accountability Act (HIPAA) is a federal law that protects private patient information from being disclosed without permission. Individually identifiable health information is protected under HIPAA in a nationwide and standardized way. HIPAA also allows for the flow of non-sensitive health data that may be used for public health and well-being.
Personally identifiable information HIPAA rules are well detailed in this law and make the protections clear to patients and guardians.
FERPA
The Family Educational Rights and Privacy Act (FERPA) is a federal law that protects student educational records. It also provides provisions for parents and students to request data and give permission to release files.
FERPA personally identifiable information protection applies to all schools that receive funds from the U.S. Department of Education. It may not apply to some private schools, colleges, or universities.
Privacy Act of 1974
The Privacy Act of 1974 established information collection practices that govern the use, maintenance, and dissemination of PII held by the U.S. Federal Government. Additionally, it provides a means where citizens can access and request the change of their records.
Some of the agencies that regulate PII handling include:
- The Network Advertising Initiative (NAI)
- The Department of Consumer Protection (part of the Federal Trade Commission)
- Consumer Affairs
- The Federal Communications Commission (FCC)
- The National Institute of Standards and Technology (NIST)
To wrap it up
PII violations can be devastating to your life. That’s why it’s so important to safeguard your information and take precautions to protect both your data and your identity.
Remember, even information not considered PII can be pieced together by cybercriminals resulting in fraud and identity theft. To avoid this, we strongly encourage you to use Onerep’s free 5-day trial to delete your personal information from people-search sites that expose your PII and other personal data.
FAQ
What is a PII violation?
The most prevalent PII violation is identity theft. But any case where your personally identifiable information is used or shared without your consent is a violation.
Who owns PII?
Companies collect PII about consumers, and they are responsible for keeping that data safe. While the information their systems contain may be about consumers, the business owns those records. In some cases, you may be entitled to view these records by request. It is your responsibility to make good choices that safeguard your direct identifiers and make wise decisions about how you share them.
Who is responsible for protecting PII?
Companies and individuals share responsibility for protecting PII. Many companies have security policies and personally identifiable information training to be sure their employees understand how to protect sensitive PII.
What must you do when emailing personally identifiable information?
PII should never be emailed using unsecured email. Use encrypted secure email systems that can not be easily intercepted by hackers who could steal any personally identifiable information.
What is the best example of protected health information?
Protected Health Information (PHI) includes PII that could identify a patient and any medical record about that person. A person’s disease history is protected from unauthorized disclosure. PHI is legally protected by the Health Insurance Portability and Accountability Act (HIPAA) and can carry penalties of up to $50,000 per violation with a maximum of $1.5 million a year.
Is a VIN considered PII?
Yes, a Vehicle Identification Number (VIN) is considered PII as it is specific to a vehicle.
Is place of birth PII?
Some experts consider your place of birth non-sensitive information. When added to your name and bank account number, it can become sensitive.
Is last 4 digits of SSN considered PII?
Yes, the last four digits of your Social Security number are sensitive PII. This truncated SSN is highly sensitive both stand-alone and in combination with other bits of PII.
Is personally identifiable information the same in each state?
There are both federal and state laws that define and regulate PII. Personally identifiable information law may vary across states. But federal laws, acts, and government agencies protect PII disclosure across the country. Additionally, different industries have regulatory organizations that mandate PII handling. PII’s meaning is consistently understood in all states, as any data that directly identifies a natural person.





Mark comes from a strong background in the identity theft protection and consumer credit world, having spent 4 years at Experian, including working on FreeCreditReport and ProtectMyID. He is frequently featured on various media outlets, including MarketWatch, Yahoo News, WTVC, CBS News, and others.